I kept hearing about the data breach at the OPM. I thought to myself, “no big deal,” because I’ve never been a government employee. But then one of the articles I read spoke about a particular form. The form number seemed familiar.
I kept hearing about the data breach at the OPM. I thought to myself, “no big deal,” because I’ve never been a government employee. But then one of the articles I read spoke about a particular form. The form number seemed familiar.
Out of curiosity I checked my encrypted drive.
AHHHH SHIT!!!!
Yep, that’s a form I filled out while I was working for a government contractor.
DAMN! Checking some of the other forms and sure enough! There’s a TON of information that I provided to my employer. I’m sure that that information got sent at some point to the OPM, and is now in the hands of the Chinese.
I’m sitting here looking at my encrypted volume that contains this information thinking a couple of things.
 First, I’m wondering why I take the security of this information so seriously? Why is it that I’ve spent the money to secure my data and theirs (some of the information contained in the forms I filled out for them also contains information that relates directly to THEIR projects) and am mindful of what data I have “live” on my system and what data I keep in cold storage? Cold storage in my life is something (like a drive) that is archival, MUST be turned on or attached directly to my computer and is encrypted.
First, I’m wondering why I take the security of this information so seriously? Why is it that I’ve spent the money to secure my data and theirs (some of the information contained in the forms I filled out for them also contains information that relates directly to THEIR projects) and am mindful of what data I have “live” on my system and what data I keep in cold storage? Cold storage in my life is something (like a drive) that is archival, MUST be turned on or attached directly to my computer and is encrypted.
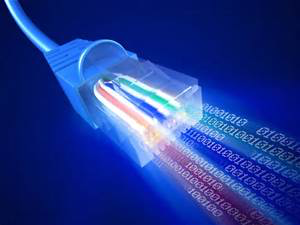
Second, If I can secure my data with COTS (Commercial Off The Shelf) software why can’t our government?
Third, Why is the United States Government data vulnerable in the first place? We KNOW the safest computers are computers which are not connected to a network. Granted, that’s impractical because the government must share data.

BUT it is possible to isolate critical subsystems. One way to do that, don’t allow employees to transport any data offsite. No USB memory sticks or other media, and laptops are available only to those employees who absolutely need mobility. Employees using those laptops have VPN access to the corporate systems and for the most part those laptops when connected to the corporate VPN are Terminals in the old school meaning of terminals. ie dumb as a rock.
The point I’m making here is that the need for computer & network security isn’t new. So why the hell hasn’t our government kept up with the needs for security?
Having seen the way government contracts work, I have a guess.
Imagine a situation where a bunch of cooks get in the soup and specify all manner of equipment down to the smallest detail. Once finished, the specification goes from committee to committee and after a year or two the spec is approved, money is appropriated and the funds become available.
Our happy IT guys call a government approved vendor of equipment, and are told that equipment isn’t available anymore. Or worse yet, the equipment or software can be purchased but now it’s a custom build and will be 50% more expensive than the original product and by the way have significantly fewer capabilities than current off the shelf products costing significantly less than the originally specified equipment or software originally sold for.

So in the one case the specification process starts over again. In the other case the “approved equipment” is less capable, yet more expensive, than the machine a hacker in China purchased on the internet yesterday.
Rather than the committees addressing the fundamental problem in terms of appropriations and approvals they’re content to keep failing. Meanwhile the security of government systems continues to fall further and further behind.
This isn’t a partisan issue. Regardless of what the administration might say. This is an epic systemic failure on the part of an entity that has access to all of our private data. A.K.A The United States Government.

How do you solve this problem?
The simplest way is to allow the IT people, The REAL IT people, not the morons that built the healthcare.gov site, say “we need a router and after figuring out which is the best unit for the money… They BUY IT!
That should go for a single router or a RACK of routers.
Does Dianne Freakin Feinstein have a clue about the difference between a CISCO and a Barracuda? NO!
So why are people like Feinstein reviewing and voting on these appropriations bills or worse yet wasting time and money having hearings about shit they’ll never understand, when they should be letting the professionals do the job? You can tell pretty darn fast if an IT dept. is pissing money away and a quarterly budget review (again by IT pros who know what’s needed and what it costs) would keep the expenditures in check and at the same time maintain security.
I’ve got another dose of BAD news for you dear reader…

The longer our leaders put off fixing the government IT infrastructure, the more expensive it’s going to be.
Think about putting off having your brakes fixed on your car.
Brake pads cost $45 a wheel, Brake ROTORS cost $1000 a wheel. Most of us average folks learn the hard lesson, it’s always better to spend the $180 rather than spending the $1180. We all learn it once!
We never make that mistake again unless we’re wealthy, elitist, over-educated, dumbasses.
Unfortunately, most of our politicians are the latter kind of people not the former.
Update 2015 06 19
As more comes out about this breach, I think it’s clear that the government IT people are not up to the challenge.
Here is a line to an ars Technica article titled Encryption “would not have helped at OPM says DHS official”
Below is the article minus the video.
Encryption “would not have helped” at OPM, says DHS official

Office of Personnel Management Director Katherine Archuleta would be happy to discuss the particulars of the OPM brief with Congress—in a classified briefing.
CSPAN
During testimony today in a grueling two-hour hearing before the House Oversight and Government Reform Committee, Office of Personnel Management (OPM) Director Katherine Archuleta claimed that she had recognized huge problems with the agency’s computer security when she assumed her post 18 months ago. But when pressed on why systems had not been protected with encryption prior to the recent discovery of an intrusion that gave attackers access to sensitive data on millions of government employees and government contractors, she said, “It is not feasible to implement on networks that are too old.” She added that the agency is now working to encrypt data within its networks.
But even if the systems had been encrypted, it likely wouldn’t have mattered. Department of Homeland Security Assistant Secretary for Cybersecurity Dr. Andy Ozment testified that encryption would “not have helped in this case” because the attackers had gained valid user credentials to the systems that they attacked—likely through social engineering. And because of the lack of multifactor authentication on these systems, the attackers would have been able to use those credentials at will to access systems from within and potentially even from outside the network.
House Oversight Chairman Jason Chaffetz (R-Utah) told Archuleta and OPM Chief Information Officer Donna Seymour, “You failed utterly and totally.” He referred to OPM’s own inspector general reports and hammered Seymour in particular for the 11 major systems out of 47 that had not been properly certified as secure—which were not contractor systems but systems operated by OPM’s own IT department. “They were in your office, which is a horrible example to be setting,” Chaffetz told Seymour. In total, 65 percent of OPM’s data was stored on those uncertified systems.
Chaffetz pointed out in his opening statement that for the past eight years, according to OPM’s own Inspector General reports, “OPM’s data security posture was akin to leaving all your doors and windows unlocked and hoping nobody would walk in and take the information.”
When Chaffetz asked Archuleta directly about the number of people who had been affected by the breach of OPM’s systems and whether it included contractor information as well as that of federal employees, Archuleta replied repeatedly, “I would be glad to discuss that in a classified setting.” That was Archuleta’s response to nearly all of the committee members’ questions over the course of the hearing this morning.
At least we found it
Archuleta told the committee that the breach was found only because she had been pushing forward with an aggressive plan to update OPM’s security, centralizing the oversight of IT security under the chief information officer and implementing “numerous tools and capabilities.” She claimed that it was during the process of updating tools that the breach was discovered. “But for the fact that OPM implemented new, more stringent security tools in its environment, we would have never known that malicious activity had previously existed on the network and would not have been able to share that information for the protection of the rest of the federal government,” she read from her prepared statement.
Dr. Ozment reiterated that when the malware activity behind the breach was discovered, “we loaded that information into Einstein (DHS’ government-wide intrusion detection system) immediately. We also put it into Einstein 3 (the intrusion prevention system currently being rolled out) so that agencies protected by it would be protected from it going forward.”
But nearly every question of substance about the breach—which systems were affected, how many individuals’ data was exposed, what type of data was accessed, and the potential security implications of that data—was deferred by Archuleta on the grounds that the information was classified. What wasn’t classified was OPM’s horrible track record on security, which dates back at least to the George W. Bush administration—if not further.
A history of neglect
During his opening statement, Chaffetz read verbatim from a 2009 OPM inspector general report that noted, “The continuing weakness in OPM information security program results directly from inadequate governance. Most if not all of the [information security] exceptions we noted this year result from a lack of leadership, policy, and guidance.” Similar statements were read from 2010 and 2012 reports, each more dire than the last. The OPM Office of the Inspector General only began upgrading its assessment of the agency’s security posture in its fiscal year 2014 report—filed just before news of a breach at a second OPM background investigation contractor surfaced.
Rep. Will Hurd (R-Texas), a freshman member of Congress, told the OPM executives and the other witnesses—DHS’ Ozment, Interior Department CIO Sylvia Burns, the new US CIO Tony Scott, and OPM Assistant Inspector General Michael Esser— that “the execution on security has been horrific. Good intentions are not good enough.” He asked Seymour pointedly about the legacy systems that had not been adequately protected or upgraded. Seymour replied that some of them were over 20 years old and written in COBOL, and they could not easily be upgraded or replaced. These systems would be difficult to update to include encryption or multi-factor authentication because of their aging code base, and they would require a full rewrite.

Enlarge / OPM CIO Donna Seymour said that systems couldn’t simply have encryption added because some of them were over 20 years old and written in COBOL.
Personnel systems have often been treated with less sensitivity about security by government agencies. Even health systems have had issues, such as the Department of Veterans’ Affairs national telehealth program, which was breached in December of 2014. And there have been two previous breaches of OPM background investigation data through contractors—first the now-defunct USIS in August of last year, and then KeyPoint Government Solutions less than four months later. Those breaches included data about both government employees and contractors working for the government.
But some of the security issues at OPM fall on Congress’ shoulders—the breaches of contractors in particular. Until recently, federal agents carried out background investigations for OPM. Then Congress cut the budget for investigations, and they were outsourced to USIS, which, as one person familiar with OPM’s investigation process told Ars, was essentially a company made up of “some OPM people who quit the agency and started up USIS on a shoestring.” When USIS was breached and most of its data (if not all of it) was stolen, the company lost its government contracts and was replaced by KeyPoint—”a bunch of people on an even thinner shoestring. Now if you get investigated, it’s by a person with a personal Gmail account because the company that does the investigation literally has no IT infrastructure. And this Gmail account is not one of those where a company contracts with Google for business services. It is a personal Gmail account.”
Some of the contractors that have helped OPM with managing internal data have had security issues of their own—including potentially giving foreign governments direct access to data long before the recent reported breaches. A consultant who did some work with a company contracted by OPM to manage personnel records for a number of agencies told Ars that he found the Unix systems administrator for the project “was in Argentina and his co-worker was physically located in the [People’s Republic of China]. Both had direct access to every row of data in every database: they were root. Another team that worked with these databases had at its head two team members with PRC passports. I know that because I challenged them personally and revoked their privileges. From my perspective, OPM compromised this information more than three years ago and my take on the current breach is ‘so what’s new?'”
Given the scope and duration of the data breaches, it may be impossible for the US government to get a handle on the exact extent of the damage done just by the latest attack on OPM’s systems. If anything is clear, it is that the aging infrastructure of many civilian agencies in Washington magnify the problems the government faces in securing its networks, and OPM’s data breach may just be the biggest one that the government knows about to date.
<END>





 I kept hearing about the data breach at the OPM. I thought to myself, “no big deal,” because I’ve never been a government employee. But then one of the articles I read spoke about a particular form. The form number seemed familiar.
I kept hearing about the data breach at the OPM. I thought to myself, “no big deal,” because I’ve never been a government employee. But then one of the articles I read spoke about a particular form. The form number seemed familiar. First, I’m wondering why I take the security of this information so seriously? Why is it that I’ve spent the money to secure my data
First, I’m wondering why I take the security of this information so seriously? Why is it that I’ve spent the money to secure my data